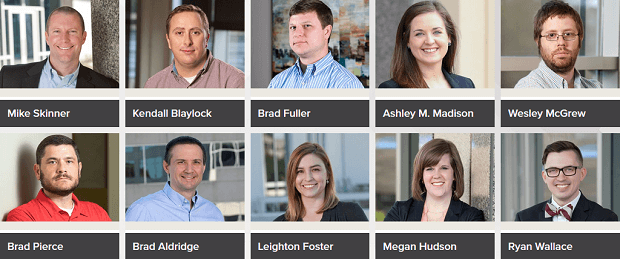
Below is our recent interview with Brad Fuller, Director of Operations at HORNE Cyber:

Q: Could you provide our readers with a brief introduction to HORNE Cyber?
A: HORNE Cyber is a highly specialized cybersecurity company focusing on advanced penetration testing and reverse engineering. Our tactics emulate advanced threats such as hacktivist groups or nation state threats. From this focus, we’ve recently launched our first product called Threat Runner.
Q: You are delivering new tools to help organizations identify their most at risk user; can you tell us something more?
A: Through our incident response and reverse engineering practice, we noticed that most organizations hit with ransomware had products in place that were supposed to stop ransomware. However, we found that larger ransomware attacks are starting with some level of system compromise that allows the attacker to bypass systems in place to stop ransomware. Threat Runner allows us to show organizations what would happen if ransomware were to bypass their defenses.
 Recommended: Technology Platform Claro Applies Machine Learning To Deliver Unique Workforce Insights
Recommended: Technology Platform Claro Applies Machine Learning To Deliver Unique Workforce Insights
Q: Can you give us more insights into Threat Runner?
A: Threat Runner is a product of our reverse engineering practice. We’ve reverse engineered different variants of ransomware and made them operate in a way that is informational to our clients. Before, you could never be 100% sure what the impact of an outbreak would be from particular user accounts. Threat Runner gives you the ability to test different users and different network ranges so that you can see firsthand what would be encrypted in a ransomware attack.
Threat Runner is constantly updated with new variants. It takes us about a week to add a simulation once we have a sample of a new ransomware.
Q: Threat Runner has added a Domain-Users Summary Simulation; what are main benefits?
A: The addition of the Domain-Users Summary simulation was a response to feedback from our clients. Our clients noted that it was difficult to know which users to focus on when running a limited number of Threat Runner simulations. The Domain-Users Summary simulation populates all accounts sorted by the level of data that they could encrypt. This allows client to better target the user accounts that need further simulation. It also allows clients to quickly find anomalies that may fall outside of what was thought to be set by group policy.
Q: What are your plans for next six months?
A: Over the next six months we will continue to add ransomware simulations to the system and improve the user experience. One addition in particular that we will launch is a simulation for the BlueKeep RDP vulnerability. We feel that this vulnerability will be used to create a wormable ransomware much like Wanna Cry, so we are constantly monitoring for it to be weaponized so that we can study the functionality and add it to Threat Runner.

 Recommended:
Recommended: 