Insignary is a venture-backed startup, headquartered in South Korea, with a strong presence in Silicon Valley. Insignary is the global leader in binary-level, open source software security and compliance. The company offers their flagship product Insignary Clarity, with the option to purchase a per/server package as either a cloud or on premise-based service. They recently introduced TruthIsIntheBinary. In both cases, Insignary’s solutions enable the scanning of software in binary format to uncover and address open source security and license compliance issues. Below is our interview with Tae Jin (TJ) Kang, President and CEO of Insignary:

Q: You’ve recently announced TruthIsIntheBinary; could you tell us something more?
A: We are very pleased with the response to our recently released TruthIsIntheBinary service. Powered by our Insignary Clarity binary code scanning software, TruthIsIntheBinary lets OEMs and developers very quickly and easily scan open source software in their embedded applications and IoT devices. It identifies SambaCry, Devil’s Ivy, Heartbleed, Ghost, and Venom, among more than 91,000 known security vulnerabilities, helping to neutralize what industry experts see as an IoT security “ticking time-bomb.”
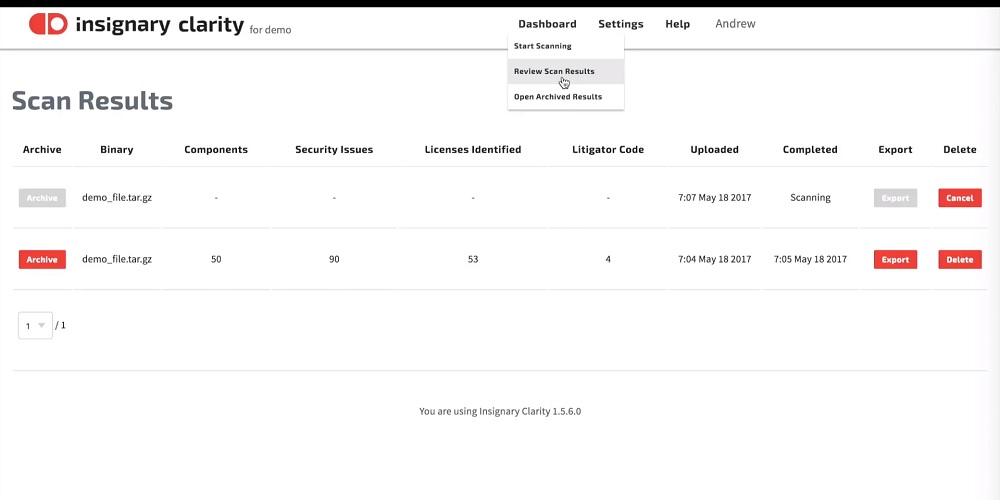
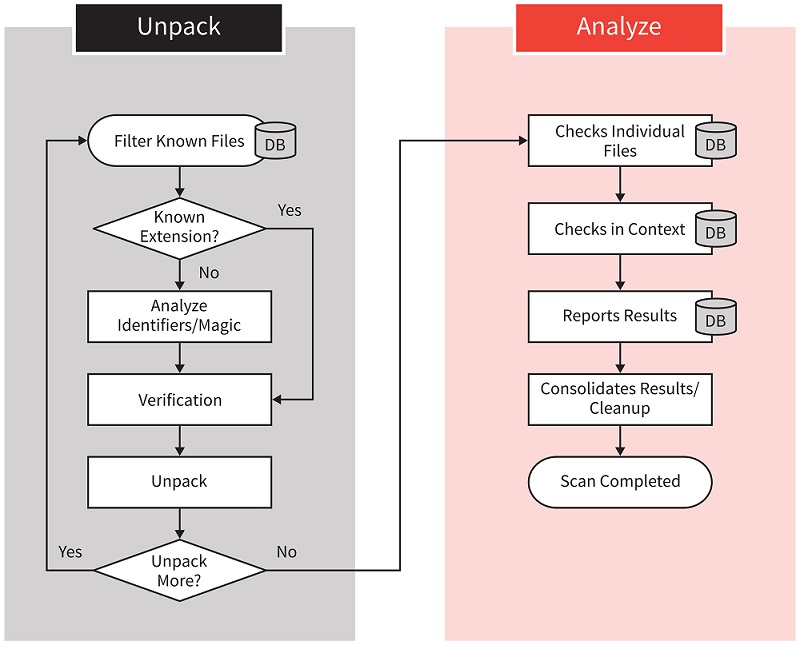
Users start by uploading an uncompressed binary file to the site. Any executable file created to run on 99% of existing computing platforms may be scanned — including smart phone apps people download from app stores. The service scans the software within a few minutes. Users receive a report of the scanned software that includes the number of potential security issues and their level of severity. With this information, OEMs and developers can look to address the security vulnerabilities with patches or newer versions of the software.
 Recommended: Technology Expense Management Platform Cimpl Provides Several Levels Of Automation To Help Businesses Save Time And Money
Recommended: Technology Expense Management Platform Cimpl Provides Several Levels Of Automation To Help Businesses Save Time And Money
Q: Can you give us more insights into your software?
A: Ninety percent of today’s applications’ software code contains open source components, and it is well known that many of the OSS components contain security issues. It is deficient, and some might go so far as to say negligent, if the code delivered to a customer contains known security vulnerabilities. With code scanners or analyzers, software developers can uncover and patch known security vulnerabilities. Doing so would significantly shore up software security.
There are a number of great source code software scanners on the market. They are great tools to leverage during the software development process. However, there are a number of reasons that companies, IoT OEMs and enterprise users want a reliable binary code scanner.
One of the issues with simply scanning the source code, is that the source code being reviewed or delivered may be out of sync with the binary on the hardware. The QA team, whose job is to make sure that the final software loaded onto the device does not contain any known issues, may be misled if they base their opinion by looking at just the source code supplied to them by the development team. The source code they are reviewing may be a different version than the actual code that the binary on the hardware is derived from. The chance of source code and binary code mismatches increases when the binary is sourced from a third party. To avoid this kind of problem, it is always better to check the final product that will be delivered and used by the end user. Namely, the binary code.
Another reason why binary scanning may be a better alternative than source code scanning is that sometimes, source code contains misleading information. One common developer habit is to leave older versions of code in the same source code file – by “commenting it out” – in case they may have to revert to it. Putting the old code in the commentary means it will be ignored by the compiler and therefore will not get included in the final binary code. However, source code scanners do not recognize this developer trick and erroneously report that the code contains multiple versions of a component. Since the old versions of the code are absent in the binary, binary scanners do not report these false positives.
We have focused the Insignary Clarity and TruthIsIntheBinary solutions to address the code that is shipped and used by OEMs and final customers – the binary. This eliminates code composition confusion, avoids false positives and uncovers the known security vulnerabilities.
 Recommended: Real-Time Innovations (RTI) Delivers Next-Gen IoT Connectivity Applications For A Wide Range Of Industrial Systems
Recommended: Real-Time Innovations (RTI) Delivers Next-Gen IoT Connectivity Applications For A Wide Range Of Industrial Systems
Q: What makes Insignary a good choice?
A: Of the several binary code scanners, we believe our advantage is two-fold. First, Insignary Clarity has greater coverage than any other scanning tools in terms of identifying correct Open Source components and versions that are present in the binary. Insignary has created a fingerprint database from more than 40,000 open source projects, whereas, our closest competition covers several thousand projects.
Second, Clarity’s identifier-based fingerprinting and fuzzy matching, allow us to identify components even when snippets of an open source component are used, or the OSS component is modified to produce the binary, whereas checksum or hash based binary scanners cannot.
There is so much commercial software out there built on top of open source components that have known security vulnerabilities. Insignary has checked the firmware of popular IoT hardware, and a significant number of them have high severity security issues. Awareness is imperative, especially because there are tools like Clarity to help counter these issues.
Q: What are your plans for the next six months?
A: We have had a very busy first half of 2017. In the second half, we will continue to enhance the Insignary Clarity and TruthIsIntheBinary capabilities – making the services more powerful for developers and OEMs. We view 2018, as a critical year for IoT development and adoption. Should the number of IoT-based security incidents continue to grow due to a lack of addressing known security vulnerabilities, we believe it will hamper IoT growth. That means we need to continue our education of the developer community now, as they build out software for next year.

