* – This article has been archived and is no longer updated by our editorial team –
Sift Security’s CloudHunter frees companies to fully and securely take advantage of cloud infrastructure in their business by providing comprehensive visibility, advanced detection, and automated response for cloud-centric applications and infrastructure. CloudHunter monitors for misconfigurations and leverages behavioral analytics to identify and prioritize advanced threats across an organization’s public, private, and hybrid cloud infrastructure, even when different cloud service providers are involved.
Below is our interview with Neil King, CEO at Sift Security:

Q:What challenges CloudHunter solves?
A: CloudHunter solves the biggest challenges organizations face when securing their cloud infrastructure – knowing what you have and where it is, whether it’s properly configured, detecting threats, and providing a simple, streamlined workflow for incident response. With CloudHunter, Security, Cloud, and Development Operations teams, along with Incident Responders can easily monitor and protect against risks. Of course, the successful solution must be nimble, allowing the organization to flexibly work across the realities of public, private, and hybrid cloud environments.
Q: What makes Sift Security stand out from its competition?
A: Many things set Sift Security apart from the competition, but here are a few that consistently resonate with our customers:
● Unlike first generation cloud security tools that focus solely on configuration management, CloudHunter identifies misconfigurations and helps you discover, investigate, and respond to active threats across your cloud environments.
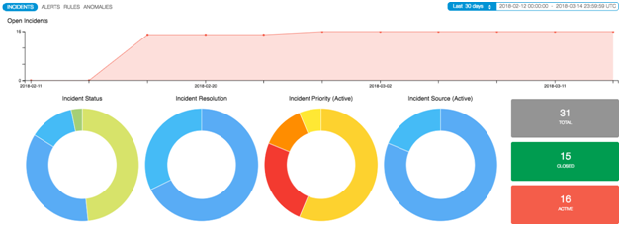
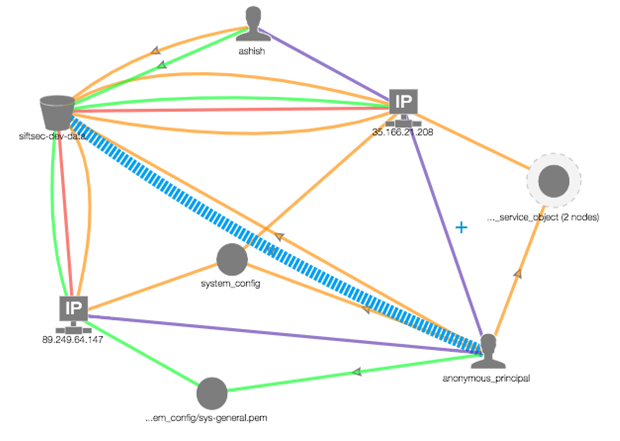
● We leverage cloud-based, situation-specific layers of behavioral detections, machine learning and graph algorithms to give CloudHunter the ability to consistently identify the high priority incidents that truly require immediate attention.
 Recommended: Sift Security Is A Pioneering Detection And Response Platform Focused On Securing Cloud Infrastructure
Recommended: Sift Security Is A Pioneering Detection And Response Platform Focused On Securing Cloud Infrastructure
● Unlike the vast majority of SIEMs and general-purpose analytics tools, CloudHunter deploys in minutes and generates immediate value. No more waiting for weeks on end to gather enough data, only to then wonder whether you are truly problem-free or if the tool is actually working.
● CloudHunter scales predictably and is value-priced, making it extremely attractive regardless of your specific environment’s configuration or breadth.
Q: Why are we doing this? What problem does it solve?
A: Companies need to establish, maintain, and demonstrate a proper security posture for their cloud infrastructure. This starts with ensuring proper configuration, detection of active threats, responding to incidents, and continues through reporting on status. This flow must work across multiple cloud instances and vendors (CSPs), delivering unified visibility to ensure ease of use and the elimination of mistakes that often arise due to differing interfaces and siloed products. Sift Security’s CloudHunter was created to do exactly that.
Q: Who benefits from Sift Security and how?
A: Organizations with sensitive data in the cloud who are looking to do more than just configuration scanning to protect their cloud infrastructure benefit greatly from CloudHunter. While the Government, Financial Services, and Healthcare verticals are common beneficiaries, we increasingly see customers with stakeholders that need evidence of strong security posture and compliance, such as Board of Directors, Regulators, Customers, and Partners.
Typically, CloudHunter supports and benefits four key personnel groups within these organizations. (1) Management is interested in visibility and reporting, (2) Security Operations needs prioritized, high fidelity alerts, (3) Incident Response needs to be able to quickly investigate and respond to threats, and (4) DevOps teams typically partner with Security to remediate risks and threats.
 Recommended: Swrve Raises $25M Series D Funding To Help Its Clients Build Highly Effective Mobile Marketing Campaigns
Recommended: Swrve Raises $25M Series D Funding To Help Its Clients Build Highly Effective Mobile Marketing Campaigns
Q: What are the key benefits of integrating Amazon GuardDuty with Sift Security CloudHunter?
A: Sift Security integrates with the infrastructure that you already have, making use of relevant data. Integrating Amazon GuardDuty with Sift Security CloudHunter delivers the following key benefits:
● Centralized & Enhanced Cloud Visibility
● Enhanced Alerts
● Entity Behavior Analysis
● Easier, Faster Investigations
● Seamless, Automated Response
Q: What are your plans for the future?
A: CloudHunter is currently available with robust support for AWS (see AWS Support) including support for Linux OS logs and 3rd party Agents. Support for key Azure services such as compute, storage, authentication (see Azure Support) as well as robust support for windows logging (Audit logs, DHCP, Domain Controller) exists today and is expanding with each release. Support for additional Cloud Service Providers (CSPs) such as Google Cloud Platform (GCP) is planned as well as adding additional cloud-based endpoint support with security features like File Integrity Monitoring.

 Recommended:
Recommended: 